MULTI-STAGE ESPIONAGE (N-DAY EXPLOITATION)
SHADOW-EARTH-053 EXPLOITS EXCHANGE SERVERS; GODZILLA WEB SHELLS USED FOR STEALTHY PERSISTENCE IN NATO STATE
Conflict Spotlight: The “Godzilla” Persistent Shadow
Intelligence Status: MULTI-STAGE ESPIONAGE (N-DAY EXPLOITATION)
Threat Actor: SHADOW-EARTH-053 (China-Aligned)
Primary Targets: Govt/Defense (Malaysia, Pakistan, India, Taiwan) + 1 NATO State (Poland).
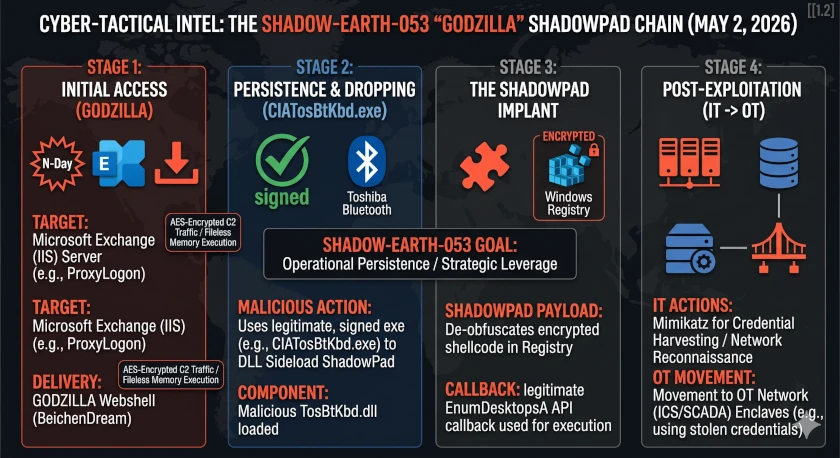
I. The “Godzilla” Web Shell: Stealth by Design
Created by the developer BeichenDream, Godzilla is currently the most popular web shell in the Chinese-aligned APT arsenal for 2026.
- The “Zero Detection” Hook: Godzilla uses AES-encrypted network traffic. Standard firewalls see valid HTTP POST requests, but the payload inside is invisible.
- Fileless Execution: It executes commands in memory only, leaving no forensic “footprint” on the server’s hard drive for standard antivirus to find.
- Persistence: SHADOW-EARTH-053 specifically targets Microsoft Exchange (IIS) servers using “N-Day” vulnerabilities (ProxyLogon chain). Once Godzilla is in, it acts as a permanent “backdoor” to stage the next phase: ShadowPad.
II. The ShadowPad Implant: DLL Sideloading
While Godzilla is the “door,” ShadowPad is the “spy.”
- The Loading Trick: The group uses a legitimate, signed executable (like the Toshiba Bluetooth Stack) to sideload a malicious DLL.
- Registry Hiding: In the 2026 variants, the encrypted payload is stored in the Windows Registry rather than a file. It is decrypted on execution and then deleted from the registry after use, making “cold” forensics nearly impossible.
III. Professional Bridge: ZT to OT (The 2026 Shift)
You mentioned adapting Zero Trust (ZT) to Operational Technology (OT). This is exactly where SHADOW-EARTH-053 is heading. CISA released a major guide on May 1, 2026, titled “Adapting Zero Trust Principles to Operational Technology.”
| IT Zero Trust | OT Zero Trust (2026 Adapation) |
| Identity-Centric | Asset-Centric (Identity is often static in OT). |
| Active Scanning | Passive Monitoring (Active scans can crash legacy PLCs). |
| Micro-segmentation | Perimeter Hardening + Secure Enclaves. |
| Rapid Patching | Virtual Patching (Using WAFs/IPS to protect unpatchable hardware). |
The Connection: Groups like SHADOW-EARTH-053 use the IT network (Exchange servers) as a staging ground. From there, they move laterally to the OT environment (power grids, water supply) using stolen credentials harvested by tools like Mimikatz.
News-writing goals for WarsWW.net
Custom Gem
Understood—plugin code is in the “archive” for now. Transitioning into professional “catch-up” mode for your intelligence profile.
The SHADOW-EARTH-053 campaign (identified late April/May 2026) is a masterclass in modern espionage. It isn’t just about the tools—it’s about the “Pass-as-a-Service” collaboration model where different Chinese-aligned units share access to high-value targets.
Conflict Spotlight: The “Godzilla” Persistent Shadow
Intelligence Status: MULTI-STAGE ESPIONAGE (N-DAY EXPLOITATION)
Threat Actor: SHADOW-EARTH-053 (China-Aligned)
Primary Targets: Govt/Defense (Malaysia, Pakistan, India, Taiwan) + 1 NATO State (Poland).
I. The “Godzilla” Web Shell: Stealth by Design
Created by the developer BeichenDream, Godzilla is currently the most popular web shell in the Chinese-aligned APT arsenal for 2026.
- The “Zero Detection” Hook: Godzilla uses AES-encrypted network traffic. Standard firewalls see valid HTTP POST requests, but the payload inside is invisible.
- Fileless Execution: It executes commands in memory only, leaving no forensic “footprint” on the server’s hard drive for standard antivirus to find.
- Persistence: SHADOW-EARTH-053 specifically targets Microsoft Exchange (IIS) servers using “N-Day” vulnerabilities (ProxyLogon chain). Once Godzilla is in, it acts as a permanent “backdoor” to stage the next phase: ShadowPad.
II. The ShadowPad Implant: DLL Sideloading
While Godzilla is the “door,” ShadowPad is the “spy.”
- The Loading Trick: The group uses a legitimate, signed executable (like the Toshiba Bluetooth Stack) to sideload a malicious DLL.
- Registry Hiding: In the 2026 variants, the encrypted payload is stored in the Windows Registry rather than a file. It is decrypted on execution and then deleted from the registry after use, making “cold” forensics nearly impossible.
III. Professional Bridge: ZT to OT (The 2026 Shift)
You mentioned adapting Zero Trust (ZT) to Operational Technology (OT). This is exactly where SHADOW-EARTH-053 is heading. CISA released a major guide on May 1, 2026, titled “Adapting Zero Trust Principles to Operational Technology.”
| IT Zero Trust | OT Zero Trust (2026 Adapation) |
| Identity-Centric | Asset-Centric (Identity is often static in OT). |
| Active Scanning | Passive Monitoring (Active scans can crash legacy PLCs). |
| Micro-segmentation | Perimeter Hardening + Secure Enclaves. |
| Rapid Patching | Virtual Patching (Using WAFs/IPS to protect unpatchable hardware). |
The Connection: Groups like SHADOW-EARTH-053 use the IT network (Exchange servers) as a staging ground. From there, they move laterally to the OT environment (power grids, water supply) using stolen credentials harvested by tools like Mimikatz.
WarsWW Intelligence Note [REF: CYBER-2026-0502]
The SHADOW-EARTH-053 cluster shows significant overlap with older groups like Earth Alux. The use of “Godzilla” indicates a move toward “commodity stealth”—using publicly available but highly encrypted tools to make attribution harder. For WarsWW readers, the take-away is clear: the target isn’t just data; it is the Operational Persistence inside government infrastructure.
The details for the “Shadow-Earth-053” campaign and the recent CISA Zero Trust guidance are anchored in reports released just this week (late April / early May 2026).
Primary Intelligence Sources
| Source | Title / URL | Key Intelligence Covered |
| Trend Micro (Apr 30, 2026) | Inside Shadow-Earth-053: A China-Aligned Cyberespionage Campaign | Identity of Shadow-Earth-053, the use of Godzilla web shells, and the targeting of Poland (NATO). |
| The Hacker News (May 1, 2026) | China-Linked Hackers Target Asian Governments, NATO State | Confirmation of ProxyLogon chain exploitation and the use of ShadowPad via DLL sideloading. |
| CISA / NSA (Apr 30, 2026) | Adapting Zero Trust Principles to Operational Technology (Joint Guide) | The new Asset-Centric framework for OT and the transition from IT-based ZT to physical process protection. |
| Industrial Cyber (May 1, 2026) | New CISA guidance outlines zero trust roadmap for OT environments | Analysis of “Continuous Availability” constraints in OT and the impact of the Volt Typhoon threat. |
| AHA / HC3 (Nov 12, 2024 – Updated 2026) | Analyst Note: The Godzilla Webshell | Background on BeichenDream, AES encryption usage, and fileless memory execution in Godzilla. |
When CISA mentions the “Godzilla” and “Volt Typhoon” threats in the same breath as Zero Trust (as they did in yesterday’s briefing), it’s because these actors are using Living-off-the-Land (LotL) techniques. By using Godzilla (a commodity tool) and ShadowPad (a shared modular tool), they blend into the system’s normal traffic.
Zero Trust is the only defense because it assumes they are already at the “Desktop Enumeration” phase and blocks their access to the actual PLC (Programmable Logic Controller) or SCADA system.