Iranian Cyber Actors Exploit US Critical Infrastructure: Tactical Coercion Amid Ceasefire
On April 7, 2026, the Cybersecurity and Infrastructure Security Agency (CISA)
issued a joint advisory (AA26-097A) confirming that Iranian-affiliated Advanced Persistent Threat (APT) groups are actively exploiting Programmable Logic Controllers (PLCs) across US critical infrastructure. The alert, co-authored by the FBI, NSA, and EPA, highlights a sophisticated campaign targeting industrial control systems (ICS) in the Water and Wastewater (WWS), Energy, and Government Facilities sectors.
Technical Breakdown: The PLC Exploit
The threat actors are specifically targeting internet-facing PLCs manufactured by Rockwell Automation and Allen-Bradley, notably the CompactLogix and Micro850 models.
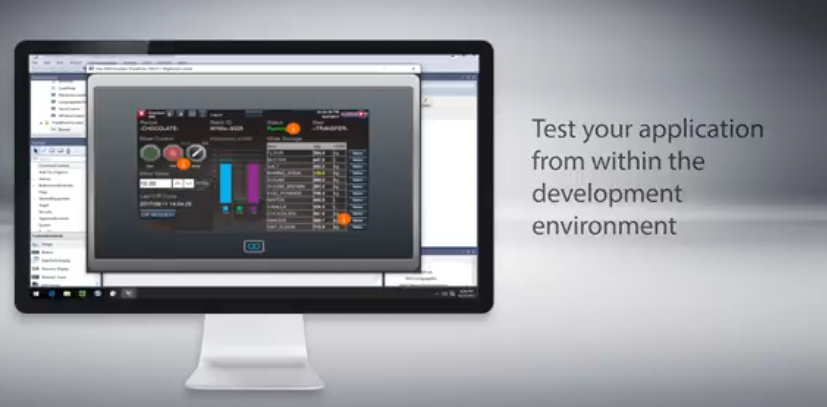
- Initial Access: Actors utilize overseas-based IP addresses and leased third-party infrastructure. They leverage specialized software, such as Rockwell Automation’s Studio 5000 Logix Designer, to create unauthorized connections to exposed devices.
- Command and Control (C2): The campaign utilizes Dropbear SSH to maintain remote access via Port 22. Analysts have also observed probes on Ports 44818, 2222, and 502, suggesting the potential for future attacks against other brands like Siemens S7 PLCs.
- Operational Impact: Observed activity includes the extraction of device project files and the manipulation of Human-Machine Interface (HMI) and SCADA displays. These manipulations can cause operators to see false data, potentially masking physical disruptions or triggering system failures.
Strategic Context: Coercion vs. Pre-positioning
This cyber escalation coincides with a fragile two-week ceasefire in the ongoing 2026 US-Iran War, mediated by Pakistan. On April 12, 2026, negotiations in Islamabad reportedly stalled as Vice President J.D. Vance departed without a permanent peace agreement.
The timing of these cyber operations suggests two primary strategic objectives:
- Coercion Signal: By demonstrating the ability to disrupt US water and energy supplies, Tehran is signaling the potential cost of a return to full-scale hostilities. This “gray zone” activity serves as leverage during high-stakes diplomatic negotiations.
- Pre-positioned Capability: The extraction of project files indicates a “reconnaissance-in-force” phase. By understanding the logic and configuration of US infrastructure, Iranian actors are pre-positioning capabilities for high-impact sabotage should the Islamabad peace talks definitively collapse.
Industry Alert: Research from Censys indicates that over 3,900 Rockwell Automation devices remain internet-exposed within the United States, leaving a significant attack surface for these state-backed actors.
Current Mitigation Status
CISA and the FBI urge all critical infrastructure operators to immediately:
- Disconnect PLCs from the public internet.
- Implement Multi-Factor Authentication (MFA) for all remote access.
- Change default passwords and audit Project File integrity.
Sidebar
The Water and Water Systems (WWS) systems are increasingly vulnerable to cyber and physical attacks, with over 52,000 drinking water and 16,000 wastewater systems serving as critical, yet often under-resourced, assets.
Water and Wastewater Sector Key Aspects
- Significance: WWS is a National Critical Function (NCF) essential for public health, safety, and the economy. It ensures sanitary services, fire suppression, and potable water.
- Threats: Increased automation has heightened vulnerability to cyberattacks, physical attacks, and natural disasters.
- Dependency: The sector relies on the Chemical, Energy, and Transportation sectors to operate, particularly for electrical power to run pumps and treatment processes.
- Resource Intensity: Wastewater treatment is highly energy-intensive, often accounting for 30–40% of total municipal energy consumption.
Energy and Government Intersection
- Energy Dependence: As energy prices rise, water utility operational costs increase significantly.
- Resilience & Security: The EPA and CISA focus on securing these systems through programs like the Water Infrastructure Finance and Innovation Act (WIFIA), providing low-cost financing for infrastructure improvements.
- Federal Role: Government facilities (including military bases and federal buildings) operate their own water systems and must comply with regulations like the Clean Water Act.
Key Security and Funding Resources
- CISA Services: CISA provides guidance on protecting water systems from hacking groups, especially with rising concerns of nation-state targeting.
- EPA Support: The EPA assists with water sector resilience through funding from the Drinking Water State Revolving Fund (DWSRF) and Clean Water State Revolving Fund (CWSRF).
- NCCoE Cybersecurity: The NCCoE is developing solutions for asset management and network segmentation.
- Water and Wastewater Systems | Cybersecurity and Infrastructure Security Agency CISAThe Water and Wastewater Systems Sector is responsible for protecting the systems that provide water and wastewater. The sector is…
CISA (.gov)
- Water Sector Interdependencies | US EPAMay 19, 2025 — The water sector has interdependencies with many critical infrastructure sectors. These sectors include:
 U.S. Environmental Protection Agency (.gov)
U.S. Environmental Protection Agency (.gov)
- National Critical Functions – Supply Water and Management – CISANational Critical Functions – Supply Water and Manage Wastewater. Ensuring the supply of safe drinking water and treatment of wastewater
 CISA (.gov).
CISA (.gov).