Weapon of Hybrid Warfare: BGP (Border Gateway Protocol) leak
The BGP route leak that impacted Namibia on January 22, 2026, serves as a stark reminder that in modern warfare and geopolitics, the most effective “blockade” isn’t always at a shipping port—it’s at the data center. While this specific incident was attributed to a configuration error, it highlights a critical vulnerability in the backbone of global communications.
For our readers at WarsWW.net, here is an expanded technical and strategic breakdown of why this incident matters in the context of international security and infrastructure resilience.
[Technical Analysis] The Invisible Front: Namibia’s BGP Fragility
1. The “Miami Connection”: Anatomy of the Leak
The root cause—a misconfiguration at a Cloudflare router in Miami—demonstrates the “butterfly effect” of global networking. In a BGP (Border Gateway Protocol) leak, a router essentially tells the rest of the world, “Send all traffic for Namibia through me.” * The Result: Traffic meant for Windhoek or Walvis Bay was suddenly diverted to Florida.
- The Impact: This created a “blackhole.” Instead of reaching their destination, data packets were dropped or trapped in “routing loops,” causing a total collapse of connectivity for essential services, including government communication and banking.
2. BGP as a Weapon of Hybrid Warfare
While the January 22nd event was accidental, the same mechanism is a primary tool for state-sponsored cyber interference.
- Prefix Hijacking: Unlike a “leak” (an error), a “hijack” is an intentional move where an adversary (such as a foreign intelligence agency) claims ownership of a nation’s IP space. This allows them to intercept, inspect, or even manipulate traffic before sending it to its destination.
- The “BGP Zombie” Threat: In times of conflict, “zombie routes” can be used to keep faulty information circulating in global routing tables even after a physical link is cut, preventing a network from self-healing.
3. Strategic Significance for Namibia & Southern Africa
Namibia is a growing hub for undersea cable landings (such as the Equiano and WACS cables). A BGP destabilization doesn’t just affect local users; it affects the regional transit of data for landlocked neighbors like Botswana and Zimbabwe.
- Infrastructure Stressors: Physical damage to fiber optic cables—often seen in conflict zones or through “gray zone” sabotage—triggers “BGP Flapping.” This is where a router continuously connects and disconnects, forcing every other router on Earth to update its map. This “churn” can degrade performance across an entire continent.
4. The Defense: RPKI and “Sovereign” Routing
To safeguard against these anomalies, Namibia is moving toward a more defensive posture:
- RPKI (Resource Public Key Infrastructure): Think of this as a “Digital ID Card” for routers. It validates that a specific network is authorized to announce specific routes, preventing 99% of accidental leaks and intentional hijacks.
- IRR-based Filtering: By using Internet Routing Registries, Namibian ISPs can create a “whitelist” of verified paths, ignoring any “shortcuts” suggested by misconfigured routers in Miami or elsewhere.
[Deep Dive] Why WarsWW.net Tracks BGP Anomalies
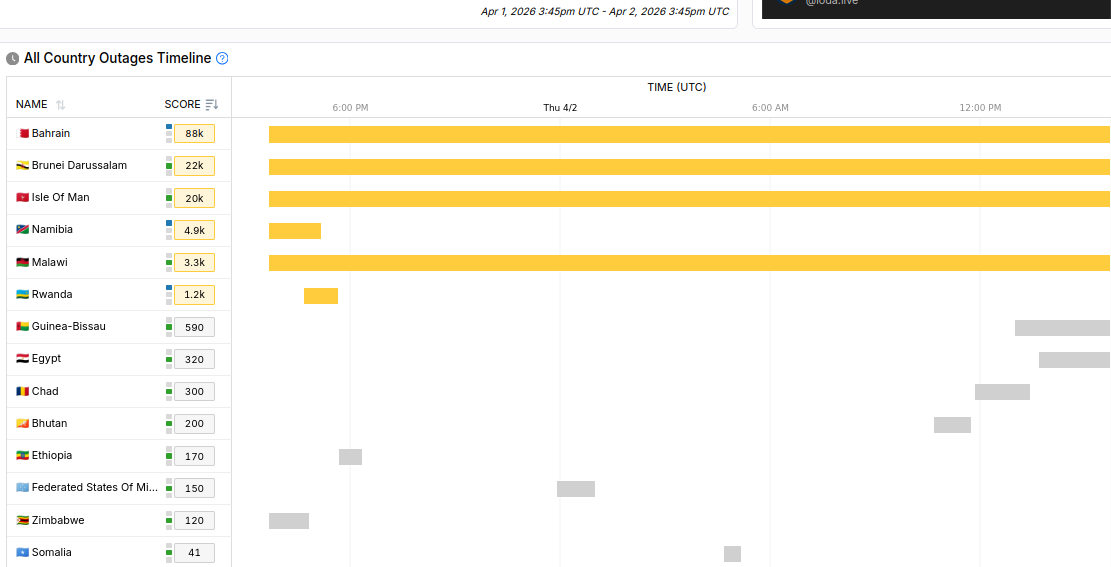
In 2026, we have seen “Digital Tolls” and “Electronic Blockades” become as common as naval skirmishes. The Namibian incident proves that a nation’s sovereignty is now tied to its routing stability.
- Intelligence Gathering: BGP leaks are often used as “tests” to see how quickly a nation can recover its connectivity.
- Economic Attrition: Just as the Houthi “Activation” in the Red Sea disrupts physical trade, BGP instability disrupts the digital economy—taxing the flow of military intelligence, open-source reporting (OSINT), and emergency response.
Editorial Note for Readers
We are currently monitoring whether any specific Autonomous Systems (AS) in Namibia—particularly those linked to government or military logistics—show signs of continued “path hunting” or underperformance. In a multi-polar world, keeping the “Digital Path” clear is the first line of national defense.
To support your guest writers and OSINT (Open-Source Intelligence) contributors, this technical checklist is designed to help them differentiate between a physical infrastructure failure and a deliberate “digital blockade” or routing anomaly.
By following these steps, your team can provide more accurate, verified reports for WarsWW.net regarding internet blackouts in conflict zones.
[Technical Checklist] OSINT Verification: BGP Hijack vs. Physical Cut
When a region suddenly goes offline, use this step-by-step process to identify the root cause before reporting.
Step 1: The “Macro” View (Global Connectivity)
Before assuming a local issue, check if the disruption is part of a larger global routing problem.
- Action: Visit Cloudflare Radar or IODA (Internet Outage Detection and Analysis).
- What to look for: A sudden, vertical drop in “Traffic” signals a physical cut or a government-mandated shutdown (kill switch). A jagged, fluctuating line often indicates BGP Flapping or severe congestion.
Step 2: Check for Route Leaks & Hijacks
If the region is “visible” but unreachable, an adversary may be misdirecting the traffic.
- Action: Use BGPStream or Cisco BGP Toolkit.
- Technical Marker: Look for “unfamiliar” upstream providers. If traffic for a Namibian ISP is suddenly being announced by an Autonomous System (AS) in a different country (e.g., Russia or China), you are likely witnessing a Prefix Hijack.
Step 3: Analyze “Latency Spikes” (The Satellite Check)
Physical infrastructure damage often forces traffic onto slower backup routes.
- Action: Run a
tracerouteto a known IP in the affected region. - The Signal: If latency jumps from 60ms to 600ms+, the primary fiber optic cable is likely severed, and traffic has failed over to satellite links. This is common in maritime conflict zones like the Red Sea.
Step 4: Verify “BGP Zombies”
In high-intensity electronic warfare, “zombie routes” can trick the internet into thinking a dead network is still alive.
- Action: Check the “Route Propagation” time.
- The Signal: If the routing table shows the network is “Up,” but no packets are returning (100% packet loss), an adversary may be re-broadcasting old routing info to mask a physical strike on a data center.
Step 5: Correlate with “Kinetic” Events
Always cross-reference technical data with on-the-ground reporting.
- Action: Check live ship-tracking (for undersea cable zones) or local social media via Starlink.
- The Correlation: Did the BGP leak coincide with a reported drone strike or a naval exercise? (e.g., The January 22 Namibia leak vs. regional maritime drills).
- [VERIFIED: PHYSICAL] – Used when IODA and traceroute confirm a cable break or power failure.
- [SIGNAL: ANOMALY] – Used when BGPStream shows unauthorized prefix announcements from foreign ASNs.
- [PROBABLE: HYBRID] – Used when a physical outage is paired with a digital “blackhole” to prevent emergency communications.